Definition
As technology has evolved and new features have emerged, new vulnerabilities have appeared alongside new technical tasks that must be addressed on a daily basis to ensure continuous improvement. With this evolution, new job roles have emerged to improve how companies operate. Today we want to talk to you about the role of the CISO within a company.
Every company with an IT department will need a CISO in its organization. To understand their duties, their day-to-day work, and the problems and mistakes they must never make, it is necessary to understand and define what a CISO is.
We have turned to Tech Target’s definition, which states: the Chief Information Security Officer (CISO) is a senior executive responsible for developing and implementing an information security program, including procedures and policies designed to protect the company’s communications, systems, and assets from internal and external threats. The CISO may also work alongside the Chief Information Officer (CIO) to procure cybersecurity products and services and manage the disaster recovery and business continuity plans. 
To understand the decision-making authority of a CISO, it is important to look at the typical organizational structure. This will vary depending on the size of the company and its needs. The CISO has an executive role and works under the direction of the CSO (Chief Security Officer), who in turn reports to the CEO (Chief Executive Officer) for decision-making. Despite this organizational structure, the role of the CISO has, in recent years, been gaining influence in business decisions. This trajectory is logical given the importance cybersecurity has acquired within digital transformation strategies.
Responsibilities
The CISO’s primary responsibility is to enhance the IT security system by closely following the company’s progress and evolution. At the same time, to grow in step with the organization, they must understand the company’s objectives and needs and adapt security accordingly so that it can improve with security and stability. This helps reduce the risk of data breaches or attacks. Changes or advancements will depend on the company’s technical, human, and financial capabilities.
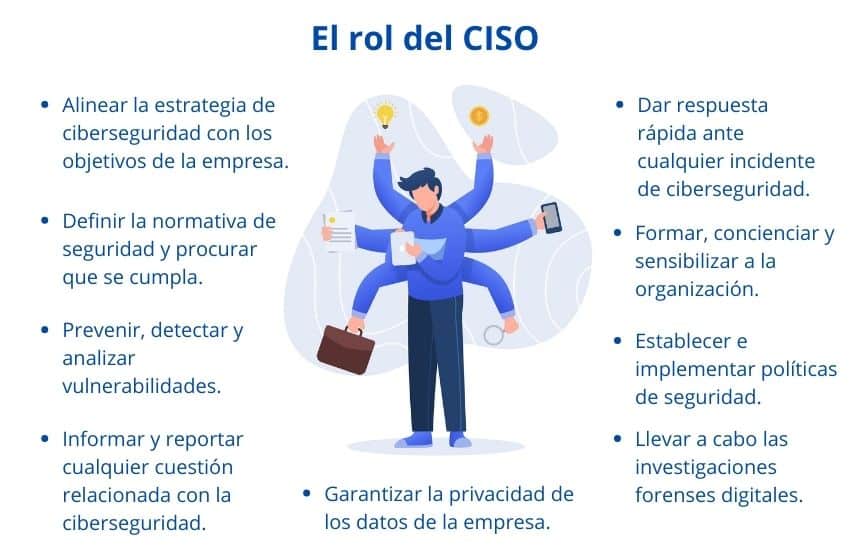
Thus, the specific functions of a CISO according to IEBS are:
- Align the cybersecurity strategy with the company’s objectives.
- Define security policies and ensure compliance.
- Prevent, detect, and analyze vulnerabilities.
- Inform and report any cybersecurity-related issues to management.
- Respond quickly to any cybersecurity incident.
- Train, educate, and raise awareness within the organization regarding information security.
- Establish and implement policies related to corporate security.
- Ensure the privacy of company data.
- Conduct electronic discovery and digital forensic investigations.
- Oversee and manage architecture, security audits, and information access control.
At the same time, they must be able to develop and train a team for the effective handover of tasks. Time is of the essence for the CISO; in cybersecurity, every second counts, which is why a smooth handover of tasks will provide more freedom to focus on priority tasks.
Another role—though it is not always recognized as such—is to convince the relevant company of the need to invest in security on an ongoing basis. This investment requires time and money but is necessary for secure long-term growth. Many experts believe that there are only two types of companies: “those that have already been attacked and know it, and those that have been attacked and don’t know it”. For CISOs, the reluctance of many companies to invest in cybersecurity is a problem. That is why CISOs must focus their attention on raising awareness, as many of these organizations still wait until it is too late to take action. Taking action only after a data breach, data loss, detection of suspicious activity, leakage of confidential documents, or other incidents has occurred is no longer effective; the damage is already done. This is where the importance of awareness lies.
It will also be important to make companies aware that relying on cybersecurity only when they have data issues or want to comply with legal requirements is not the solution. Companies solve the problem but do not delve deeper into their security to improve it.
“66% of CISOs worldwide believe their organization is not currently prepared to handle a cyberattack, with 53% in Spain,” according to the Voice of the CISO study conducted by Proofpoint
Tasks of a CISO
The tasks a CISO must perform are extensive and critical, and they cannot spend all day reviewing minor details and generating reports. These tasks are very important, but those processes can be handled automatically or by the team. That is why a good team is so important. In cybersecurity, no single element can be overlooked, and everyone is necessary.
The regular daily tasks a CISO should perform are:
- Meet with their team. It does not need to be an in-person meeting, nor does it need to be a long meeting. This meeting serves as a first check-in each morning to review ongoing projects, assign roles, and delegate daily tasks with their respective deadlines.
- Manage email. This should be done daily, with the goal of clearing the inbox.
- Recognize a job well done. This is an important task for keeping the team motivated and united so that they feel recognized and valued.
- Spend some time working alone. In the day-to-day life of a CISO, not everything should be meetings. Time alone is also necessary to analyze, think, review, define strategies, etc.
- Stay up to date on client and supplier relationships. Although it may not seem entirely necessary, it is important that you, at the very least, know which clients you are working with and what their needs are. This allows you to create or launch projects tailored to the scale or needs of the clients.
In their daily tasks, CISOs have shifted to the following paradigm, where they prioritize prevention to transition to daily detection and response.
Errors and Problems
In the role of CISO, any error can turn into a disaster for the company. That is why you must be prepared for any situation, planning ahead and acting appropriately.
The team at CSO España put together a document featuring the ‘Key Mistakes That Take a Toll on the CISO’ in which they highlight the 5 most common mistakes to watch out for. Among these are:
- Failing to prevent a data breach. In an era where digitalization is advancing by leaps and bounds, data has become the most valuable asset of any company. It is crucial to protect it and be aware of its importance, as breaches can severely damage a company’s reputation.
- Taking responsibility for risks and failing to communicate them. CISOs who assume full responsibility for the company regarding risky decisions put their jobs at risk. You must assess what the company will and will not tolerate from a security, risk, and compliance perspective.
- Inability to achieve or maintain compliance. CISOs must be able to comply with regional and national laws such as the GDPR or the LOPD. They must work with all departments to ensure none of them violate these laws.
- Unprofessional conduct. By the CISO and their staff. If the CISO is unable to correct or address inappropriate behavior, such as harassment, this could lead to the CISO’s dismissal. Unprofessional behavior can also include actions such as tweeting or expressing questionable opinions on social media.
- Inability to ensure reliability and availability. When there is an IT problem, the company—or part of it—often has to shut down, resulting not only in financial losses but also in lost time, and time, nowadays, is money. If a CISO is unable to prevent or, in the worst case, recover from the damage, problems could arise.
Another challenge CISOs face is the trend toward BYOD (Bring Your Own Device). This new modus operandi creates many vulnerabilities because personal devices are used simultaneously for work and everyday life. Devices must be protected, and it is the CISO’s responsibility to raise employee awareness and protect their work devices, thereby safeguarding the company. The organization must also provide protection systems such as antivirus software for all devices or supply directly protected software.
Shadow IT, also related to BYOD, is also a cause for concern. Shadow IT refers to any device, software, or IT service—generally cloud-based—that is used within an organization but is outside the control of the organization’s IT department or is used without its knowledge or approval. The CISO is responsible for protecting without hindering employees’ day-to-day work and for providing tools that the business also approves of. The use of third-party sharing tools such as email also causes headaches because, although it is very useful for messaging, it lacks the necessary protection for organizations.
According to Microsoft, 90% of cyberattacks start with an email.
Human error can also lead to serious problems within an organization, whether through deliberate data leaks, clicking on malicious links (via email or the web), downloading compromised files, weak passwords, or other causes. These actions put companies at risk on a daily basis.
According to the ICT Director 68% of CISOs in Spain still consider human error to be the greatest cybersecurity vulnerability in their organization.
Recommendations for CISOs
ComputerWorld states: the recommendations that can be made to each and every company are that they allocate a portion of their annual budget to meet the company’s cybersecurity needs, that they raise awareness among all staff about the associated risks and train them on these topics on a regular basis, that they have and/or design Security Master Plans, and that they have in-house or outsourced personnel qualified in cybersecurity matters whom they can consult or turn to in case of need.
According to a survey conducted by the consulting firm Ernst and Young, 87% of the organizations that participated said they did not have a sufficient budget to achieve the levels of cybersecurity and resilience they sought. The lack of resources means that companies cannot hire enough cybersecurity talent or implement the technical measures they need to counter attacks.
More and more CISOs are opting to hire a cybersecurity. These provide ‘post-attack’ protection. They assist organizations not only with financial compensation but also, in the event of theft or extortion, with negotiations.
Byte It offers 4 recommendations for CISOs:
1. Prioritize risk.
2. Plan cybersecurity tools.
3. Strengthen the basics.
4. Acquire tools and capabilities at the appropriate scale.
Alex Manea (BlackBerry) recommends: “My advice to CIOs and CISOs is to think like a hacker”
Many CISOs are already turning to external tools to enhance their company’s security.
Tranxfer is the tool of choice for CISOs to combat Shadow IT and strengthen their security strategy for file sharing, avoiding GDPR penalties and data leaks through cloud tools:
- Send and receive files securely
- Choose your sending preferences and
- Display
- Prevents malware from entering and leaving
- Controls data leaks
- End-to-End Encryption

Over 1 million licensed users
Over 5 million subscribers
Contact us for more information: info@tranxfer.com
Or through our social media:
Sources:
https://cso.computerworld.es/alertas/errores-clave-que-pasan-factura-al-ciso
https://cso.computerworld.es/pubs/cso21/index.html?page=40
https://red.computerworld.es/actualidad/que-hace-un-ciso-en-su-dia-a-dia
https://cso.computerworld.es/tendencias/el-ciso-cada-vez-mas-presente-en-las-decisiones-de-negocio
https://searchdatacenter. techtarget.com/es/definicion/CISO-director-de-seguridad-de-la-informacion
https://www.audea.com/la-figura-del-ciso-funciones-e-importancia/
https://arandasoft.com/tareas-que-un-cio-debe-cumplir-todos-los-dias/