Cybercriminals never rest. It is increasingly important to be prepared for the new challenges looming on the horizon of information security. One such challenge is the lack of security in external file sharing, which poses a potential risk of compromising the confidentiality and integrity of corporate data. Furthermore, this problem also fuels the rise of Shadow IT
What is shadow IT?
It is a practice in which employees use unauthorized applications and services for file sharing, further jeopardizing the security of the company and its information.
The importance of securing external file sharing
In an increasingly connected and globalized business environment, file sharing with business partners, suppliers, and external customers is essential for the efficient functioning of business operations. However, this file sharing carries an inherent risk of leakage or loss of confidential data. The challenge in 2024 will be to strengthen security in this process, ensuring the confidentiality, integrity, and availability of data throughout the file’s entire lifecycle.
File Sharing and Shadow IT
For security reasons, many companies restrict external access to their repositories. This creates problems for employees, who end up looking for efficient (and often insecure) ways to do their work. This may include using instant messaging apps, cloud services, or personal email accounts to send confidential work files. Shadow IT poses a significant risk to companies, as it can undermine established security controls and expose the organization to cyber threats and data breaches.
Solutions to Address File Security Challenges
To address these challenges, it is essential to implement a comprehensive file security strategy that protects both external file sharing and prevents Shadow IT. Here are some key measures to consider:
- Establish clear security policies and communicate them to all employees
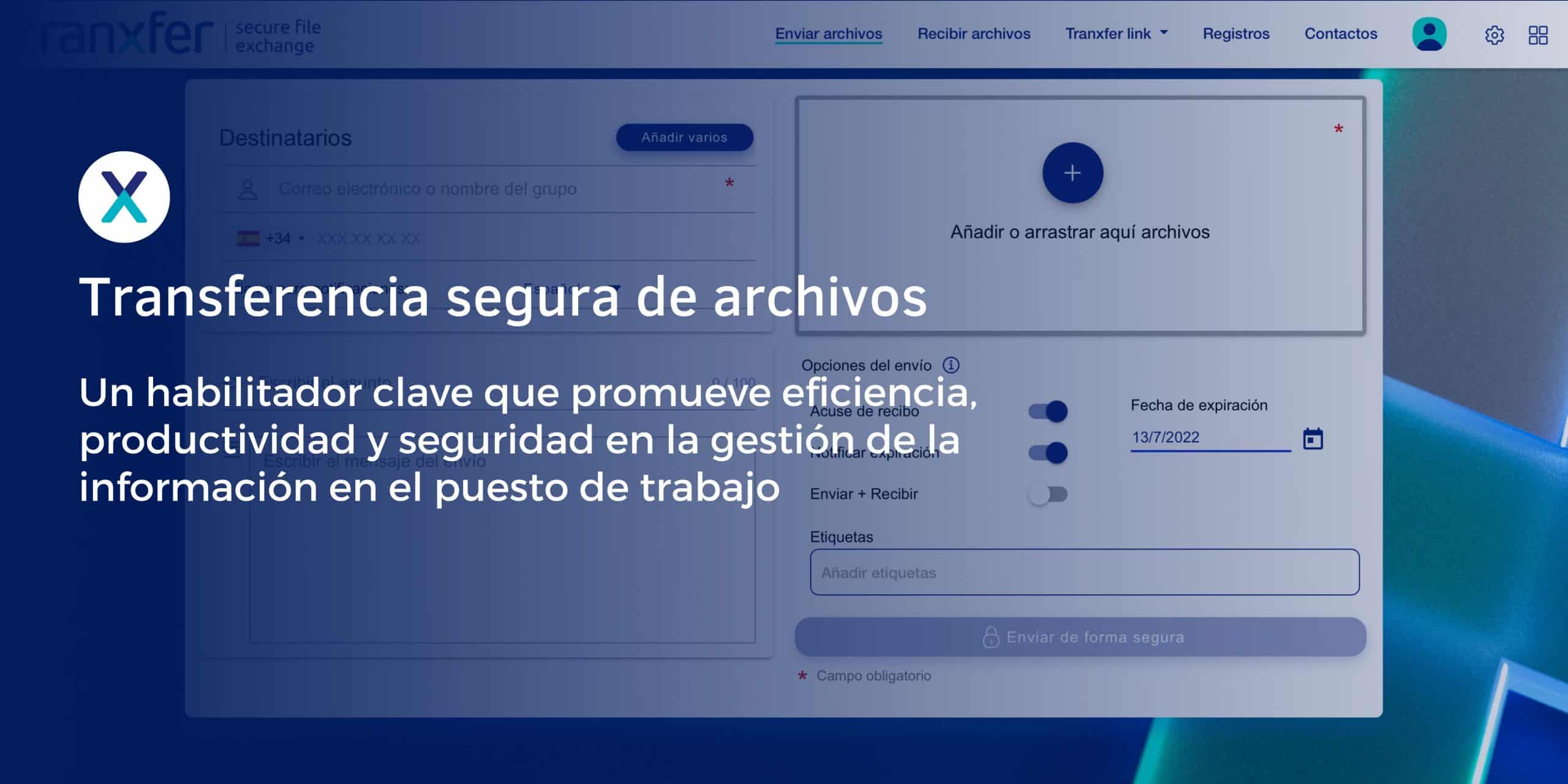
- Implement a secure file-sharing tool
- Monitor and control Shadow IT
At Tranxfer, we are committed to helping companies overcome the cybersecurity challenges of the future. Our approach is based on security, collaboration, and innovation. We partner with you, providing reliable and efficient solutions to protect your business data. Interested?
You can also subscribe to our newsletter to stay up to date on the latest news