Having an enterprise DLP can save a company’s security managers a lot of headaches and money. Why?
Today, the most valuable asset companies have is information. This information is present throughout every part of a company, whether in the form of:
Employee or candidate information managed by the HR department (Internal Information).
Information about a company’s customers managed by the sales department (Confidential Information).
The company’s strategic information for the next 5 years that the CEO must present at a shareholders’ meeting (Secret Information).
Or any other information for which a company controls the timing of publication (Public Information).
This information, which exists in the form of data, consists of files, records, and documents that need to be shared or sent to people outside the organization—such as suppliers, customers, or other stakeholders—with whom the organization collaborates to make the most of that data.
For example, in the banking sector, a potential customer of the institution who wishes to take out a mortgage, or in the healthcare sector, a laboratory that shares the results of a clinical trial with the patient.
Data Breach
Information protection is based on three basic principles:
- Confidentiality – Information accessible only to authorized individuals or systems.
- Integrity – Free from errors or unauthorized modifications
- Availability – Accessible when needed by authorized individuals or systems
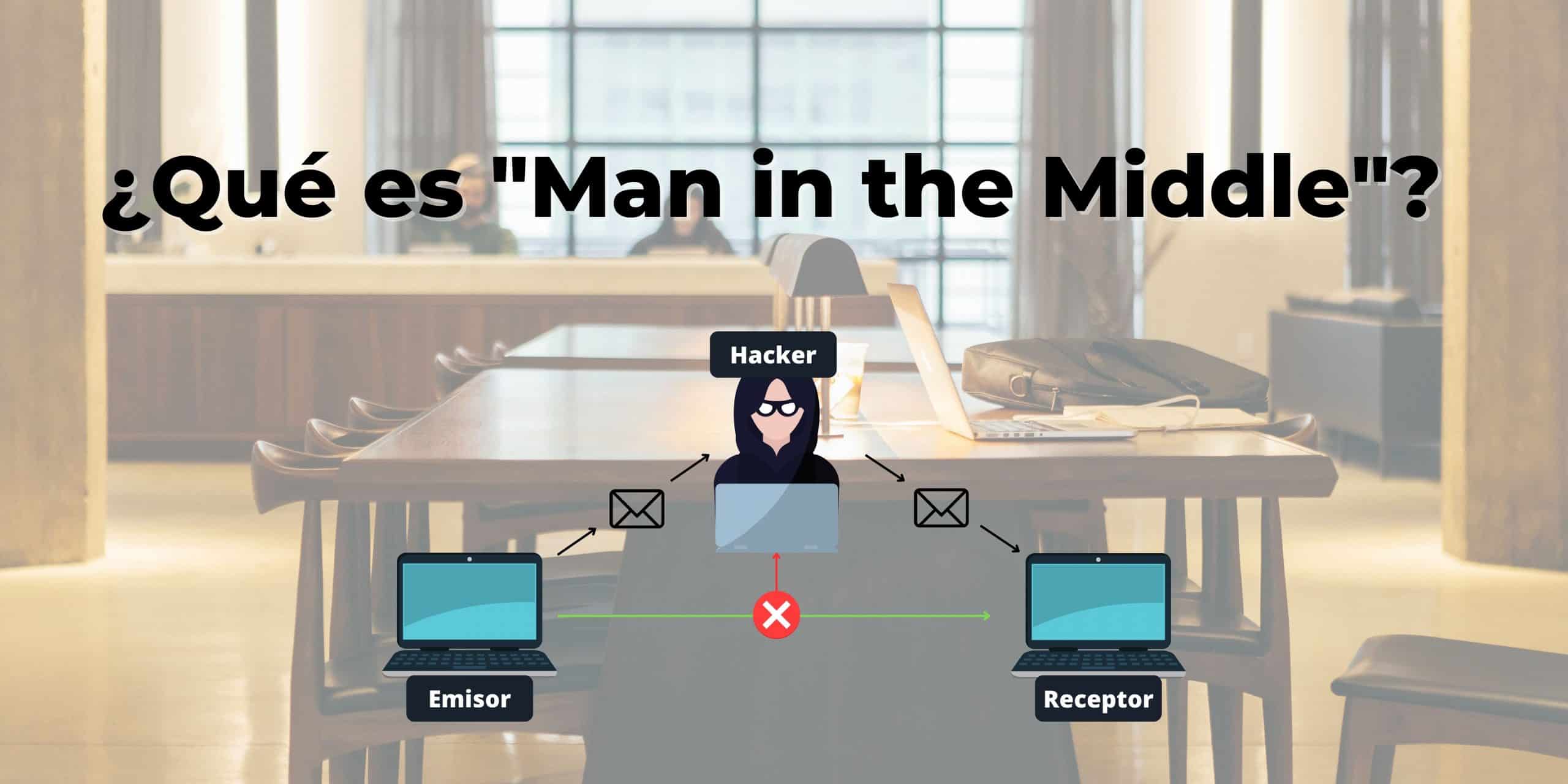
When an information leak occurs that results in a decrease in confidentiality caused by a security incident. This incident may have an internal or external origin and may be intentional or unintentional. The party responsible for safeguarding the information may detect a loss of its integrity and/or availability.
According to a study by Acronis,
76% of organizations experienced business disruptions and data loss in 2021 as a result of general system failures, human error, and cyberattacks
Three out of four companies categorize the failures that caused data loss as follows:
- General system failures (52%)
- Human error (42%
- Cyberattacks (36%)
- Internal attacks (20%)
In a study conducted by IT Governance highlighted that in 2021, organizations suffered 292 data breaches due to employee errors. The most common cause is accident and/or negligence. This includes errors such as sending information to the wrong person, or leaving physical or digital files in a public place. These causes account for 51% of all data breaches in the study.

Tranxfer … close the wall!!
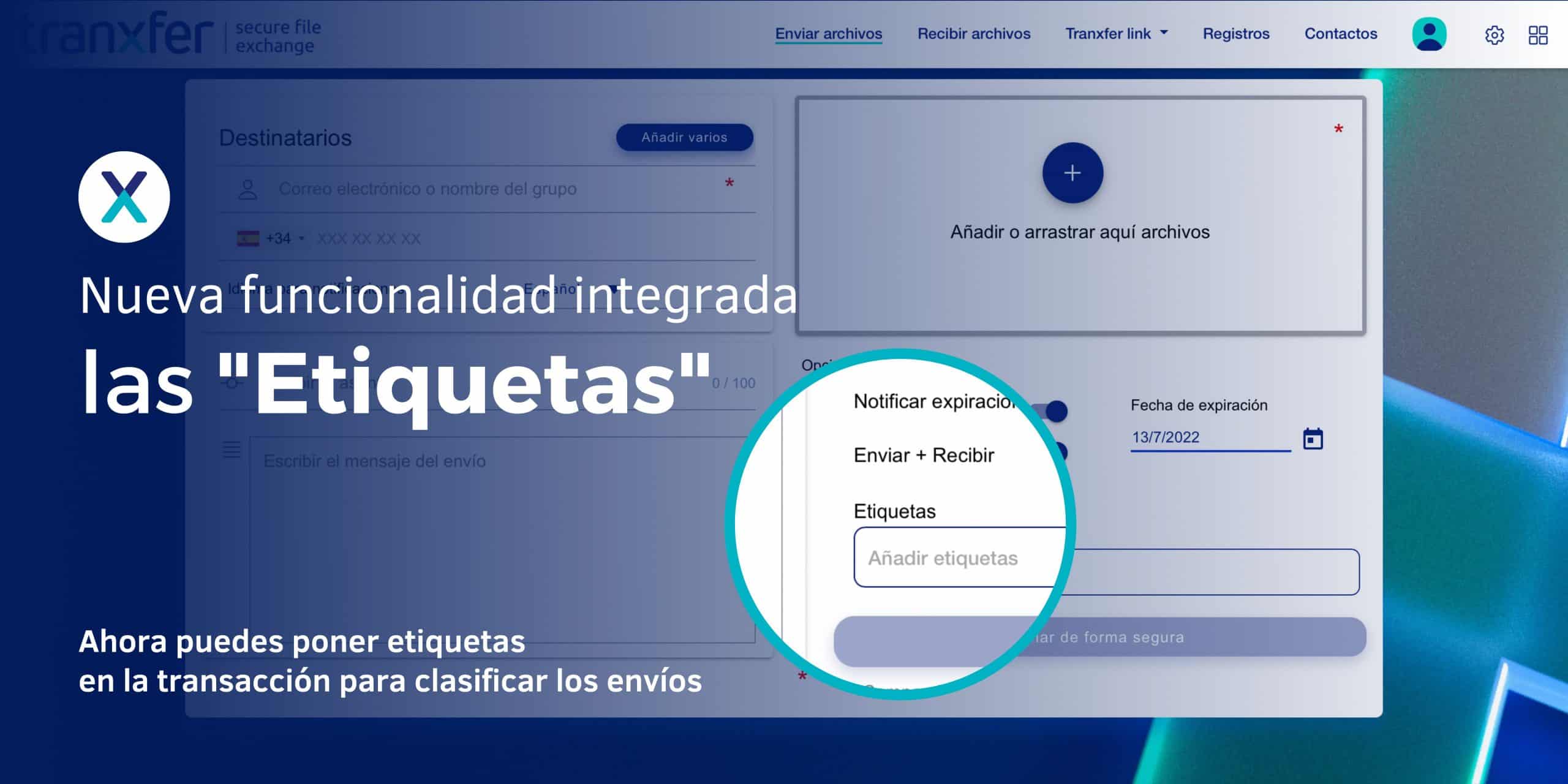
Tranxfer is a platform designed to help companies send and/or receive relevant information from other companies or individuals in the form of files. It provides users with a secure means of communication internally or with third parties, helping data and IT security managers control and minimize data leaks from companies.
As such, it offers a data leak prevention module where the client can configure the control rules that form the security policies necessary to close the wall against potential human errors and minimize this type of breach.
How to configure Tranxfer’s DLP
To configure a security rule in Tranxfer, you must access this DLP module and use the Add option to create the first rule.

This takes us to a screen where we can configure the first rule:

- Protection Type
- Global
The rule applies to the entire company - Group
The rule affects the specified user group
- Global
- List
- Black
If the regular expression matches the rule’s expression, the rule is violated. - White
If the regular expression does not match the rule’s expression, the rule is violated.
- Black
- Policy type
- File content
Validation of the regular expression against the file’s content - Recipient
Validation of the regular expression against the transfer recipient; this can be an email address or a domain. - File metadata
Validation of the regular expression against the file’s metadata tags. - File name
Validation of the regular expression against the file name; this can be the file name and/or its extension. - File type
Validation of the regular expression against the MIME type of the file.
- File content
- Validation
- Keyword/Regular Expression
The regular expression or the value of the field with the same name is evaluated. - CCC
The predefined regular expression is evaluated to find checking account numbers. - Cards
The predefined regular expression is evaluated to find debit or credit card numbers. - ID Number
The predefined regular expression is evaluated to find ID numbers. - IBAN
The predefined regular expression is evaluated to find IBAN numbers.
- Keyword/Regular Expression
- Regular Expression
Character string or regular expression containing the value or character pattern to be evaluated. - Specific
- Tags (File metadata)
Specifies the name of the tag, whose value will be evaluated against the value specified in the Regular Expression field. - Maximum allowed repetitions for blocking (File Content)
Maximum number of times a File Content rule can be violated before the rule is triggered. - Maximum number of repetitions of the same value for blocking (File content)
The maximum number of times a File content rule can be violated with the same value before the rule is considered violated.
- Tags (File metadata)
- Send notification/alert
Specify the recipients who will receive non-compliance alerts via email. - Exceptions
Specify the users or user groups that are exempt from this rule.


From this section, you can configure additional features for controlling files sent or received using the Tranxfer platform.
Content Validation on Receipt
Normally, file content validation is performed from inside to outside the organization, thereby controlling sensitive data in documents that may violate a security policy. There is the option to enable this in the opposite direction.Password-protected files
Additionally, password-encrypted files that prevent both the module itself and the antivirus from functioning properly can be validated.Files with macros
The final option for validating documents is to check whether or not they contain macros.Notification/Alert
Additionally, from this same panel, you can specify that alerts or notifications of violations be directed to one or more users or to a group of users.
When a rule is violated, the user performing the operation is notified.

This is how it regains control of the data…
Like the popular song from the mid-70s, in the face of possible breaches of security policies TunTun, who is it? … (Tranxfer) Close the wall.