Shadow IT: The Nightmare for Businesses
We live with it, but unfamiliarity with the term means we don’t know exactly what we’re referring to when we hear it. Yet Shadow IT is a common occurrence, and it’s a problem faced by businesses worldwide—one that may pose a greater threat than it appears.
But what exactly is it? How does this situation arise? What does it mean for organizations? Below, we shed light on all these questions.
The term Shadow IT refers to any technological element (hardware, software, cloud, etc.) used by a user without authorization or the knowledge of the organization’s IT manager. In other words, when an employee makes decisions on their own without consulting their supervisor and decides, for example, to use a cloud-based service without first discussing it with the company.
Data Breaches and Leaks
As is customary, every company provides its employees with equipment and software, but many employees also download and install other programs that are not monitored by the IT department. Approximately 82% of companies are unaware of all the applications their employees use on a daily basis.
This practice is more common than we currently realize. According to IBM Security, “One in three employees shares and uploads corporate data to third-party cloud applications,” and “one in four logs into cloud solutions using their corporate username and password.”
The term Shadow IT refers to any technological element (hardware, software, cloud, etc.) used by a user without authorization
With the rise of remote work, employees have been using their own devices—such as smartphones or personal laptops—for work-related tasks, indirectly sharing corporate documents through cloud storage, unauthorized networks, unmonitored computers, or third-party SaaS applications. It is worth noting that only 7% of these free internet applications meet minimum security standards, so people who use them unwittingly expose the organization to risk.
Why it happens and how to manage it
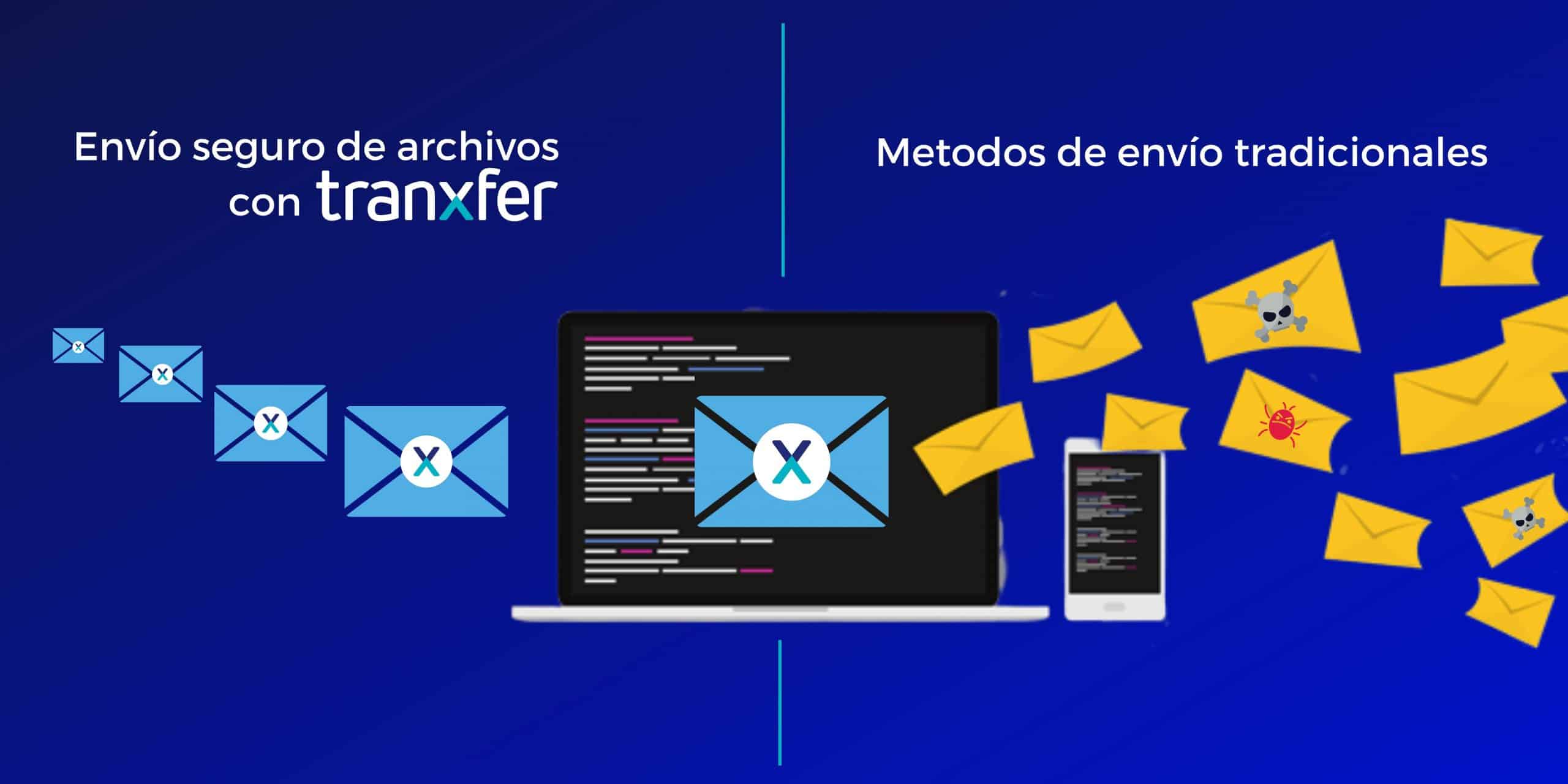
These types of situations mainly occur because the user needs to resolve a specific issue. For example, when an employee needs to send several large files that cannot be attached to an email due to their size, or when they need to perform a specific task that their computer does not support.
At first glance, all of this may seem to offer a number of advantages, such as immediacy, autonomy, and efficiency in the workplace; we might even come to believe that it translates into savings for our company. But nothing could be further from the truth. The truth is that Shadow IT leaves the door open to chaos, data leaks, theft of confidential information, and a host of vulnerabilities that result in a nightmare of costs, inefficiencies, and even a complete shutdown of business operations.
How the CISO Can Combat Shadow IT in the Company: Tips and Recommendations
The best way to combat the threats and risks of Shadow IT is by implementing guidelines, best practices, policies, and initiatives managed by the IT team—and increasingly by the CISO (Chief Information Security Officer)—that are commensurate with the company’s technical and budgetary capabilities and business needs. Some key steps to regain control across different areas of action include:
1) Analyze processes and work methods: This task is more typically the responsibility of a company’s departments rather than the IT manager. It involves periodically reviewing how each department operates and the needs of their work processes. This analysis will allow us to determine whether existing technological tools are sufficient or if new elements need to be incorporated into their work methods. This is where we can determine whether these necessary new technological elements comply with the required security measures and ensure they are identified and under control.
2) Inventory and monitoring: It is important to maintain an inventory of hardware, software, and cloud applications, and to have network monitoring, analysis, and verification methods in place that allow us to ensure that the configurations of our technological components have not been altered. For example, MDMs (mobile device management) allow us to manage an organization’s hardware and software fleet remotely, monitoring the applications in use and those that can be installed at all times. Firewalls and IDSs will allow us to monitor our network traffic.
3) Identify and act: as soon as we detect a threat, we must analyze and assess its benefits, drawbacks, and impact on the business. Adopting the new element may provide a solution and an improvement, but we must weigh the possibility that a safer and more optimal alternative exists to perform the same function.
4) Raise Awareness: An important initiative involves training employees on security issues so they understand that their actions can pose significant risks to the company. Employees must realize how dangerous actions carried out in secret—without informing our IT manager—can be.
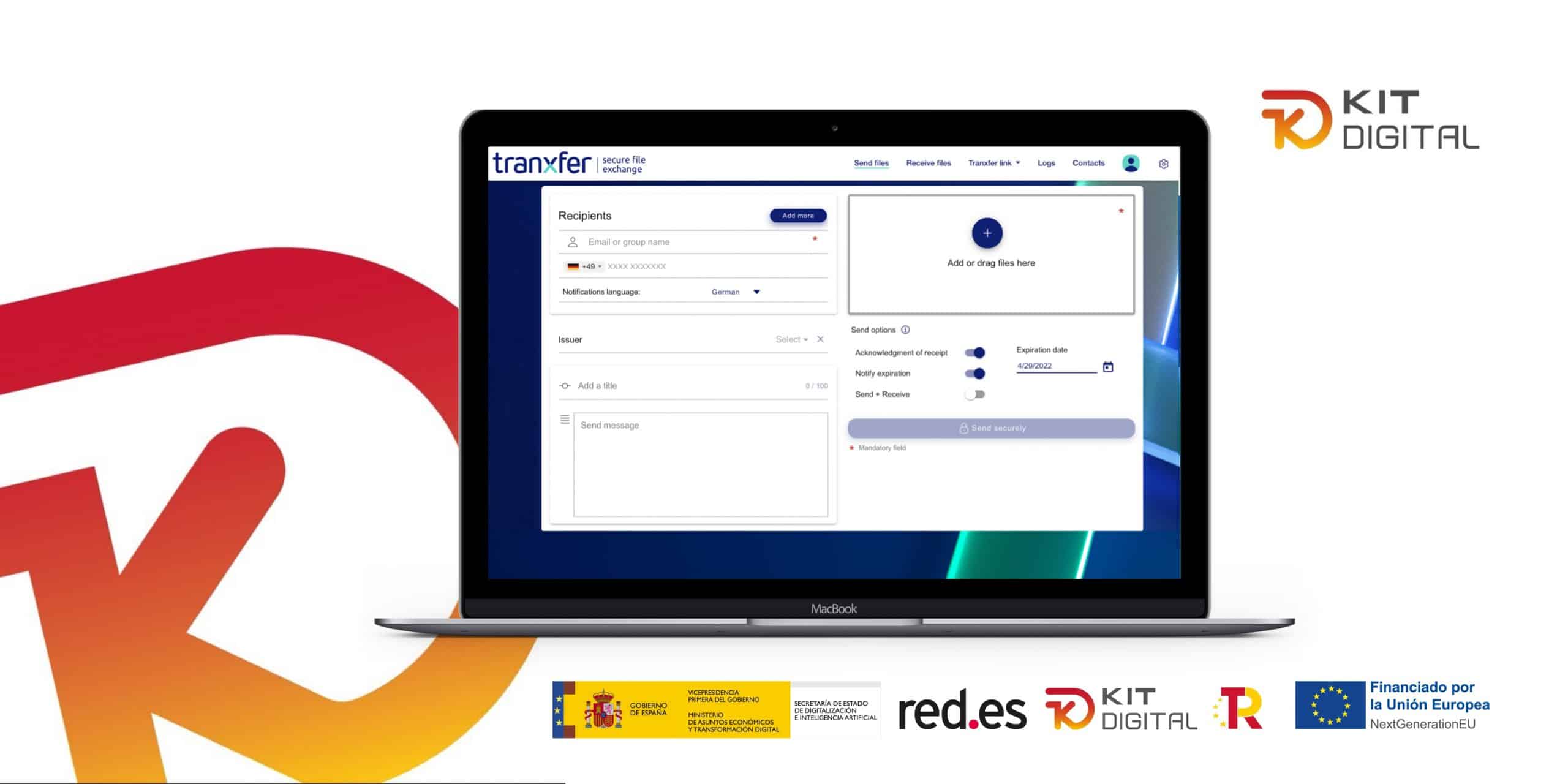
However, the most important key to managing and putting an end to these types of situations is having tools that eliminate shadow IT from companies. Ultimately, it is essential to have solutions that allow for the secure, monitored, audited, and efficient management of employee file transfers.