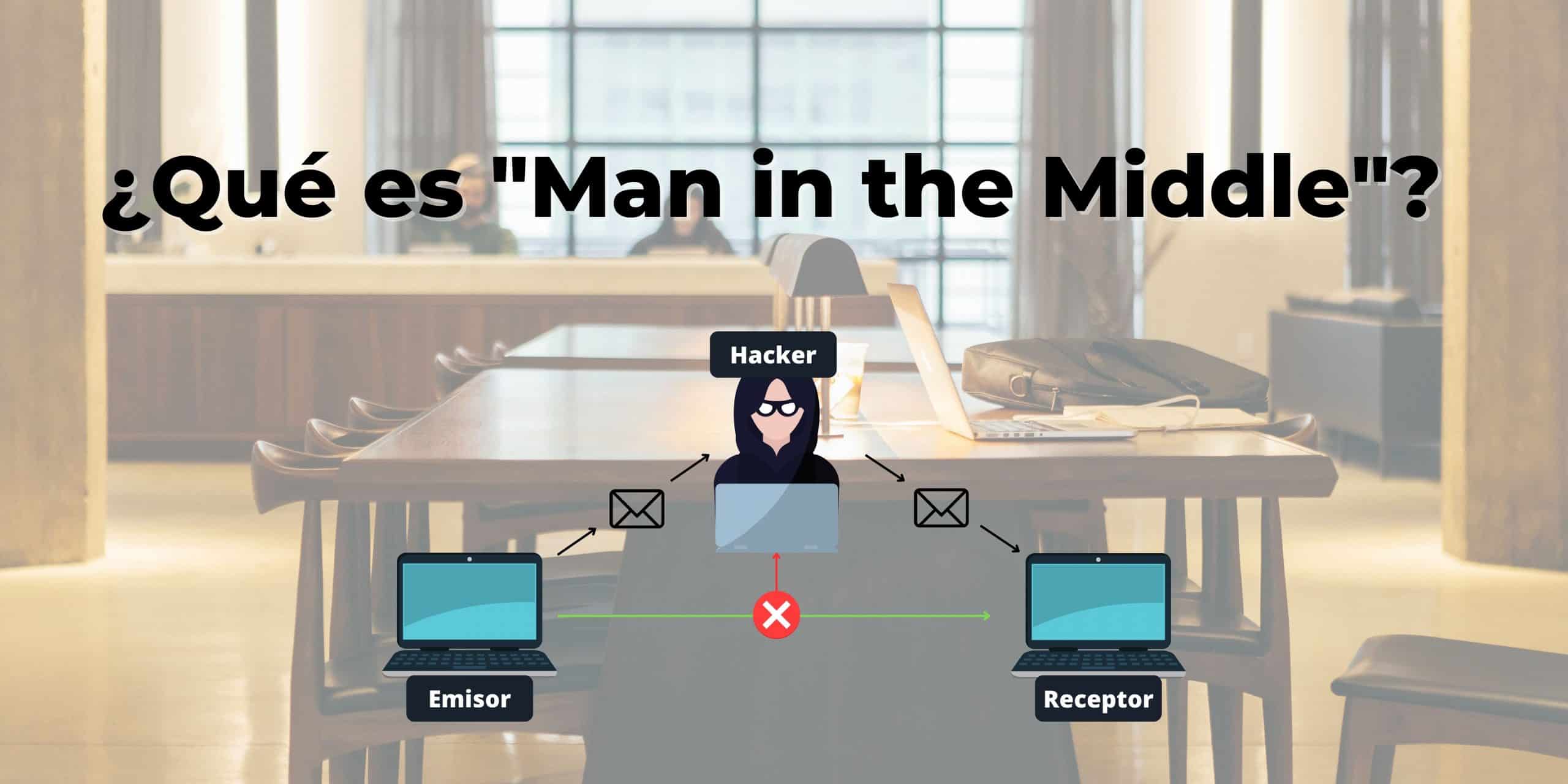
What are “Man-in-the-Middle” attacks? As the name suggests, these are cyberattacks in which a hacker positions themselves between the sender and the receiver, intercepts the message, and alters it. This is how hackers managed to steal 1 million euros from an Israeli startup, ultimately driving it into bankruptcy.
The attack intercepted communications between the venture capital firm and the startup, thereby canceling a face-to-face meeting between the two, and altered the account number included in an email for the funds transfer. The venture capital firm deposited the amount into a fake account controlled by the hackers, believing it to be the startup’s account. (access the full article)
How is it done?
How is it done? There are different ways to carry out the hack, but the goal is always the same. Tointercept the message and modify it before it reaches its recipient. The message is routed through an unsecured network controlled by the cyberattacker, and the communication is routed through a network under their control. For example, broadcasting a Wi-Fi network with an SSID similar to that of the authorized network, and attempting to get devices to connect to the unsecured network.
How does Tranxfer help mitigate these types of attacks?
Tranxfer offers a secure channel that completely eliminates this cyberthreat thanks to its advanced security policies. Files sent via Tranxfer are transmitted using end-to-end encryption. This ensures that you receive the genuine version of the file and that no one else is intercepting the communications. At Tranxfer, we want to raise awareness that cyber threats are real and much more common than is generally believed. It is vital to equip your organization with an IT security framework to prevent it from becoming an easy target for cyberattackers.
In these cyberattacks, the hacker or cyberattacker intercepts the message while it is in transit between the sender and the recipient. These attacks are difficult to detect because the sender appears to be who they claim to be, and the message arrives through normal communication channels and with the expected tone. The only difference is that the hacker or cyberattacker has intercepted the message and modified it for their own benefit. This was one of the top 5 most common causes in 2021. Its equivalent in the offline world would be the mail carrier altering a letter before delivering it to the recipient. Request a meeting with us and we will review your case