Red Team, Blue Team & Purple Team. Action, Defense, and Assessment
The cybersecurity sector is constantly evolving, and it is necessary to be prepared for every possible situation that may arise. That is why there are different cybersecurity teams: the Blue Team, the Red Team, and the Purple Team. Each has a different role and is used to assess and analyze potential system vulnerabilities.The terms Red Team and Blue Team are commonly used to describe teams that use their skills to assess a company’s cybersecurity defenses. Either mimicking the attack techniques that “enemies” might use (red team), or teams that use their skills to defend (Blue team). In fact, these teams play an important role in defending against advanced cyberattacks that threaten business communications, confidential customer data, or trade secrets.When it comes to cybersecurity and data protection, these two teams are essential. This is because they work together to detect vulnerabilities, prevent cyberattacks, and simulate threat scenarios.To understand in detail how each team works and what its functions are, we will describe each one:
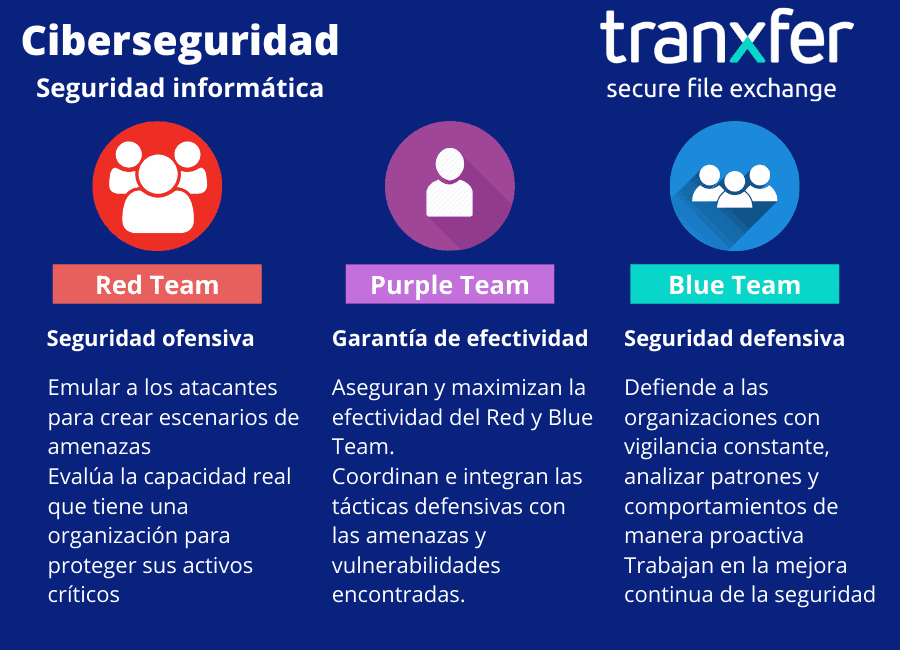
Red Team
How Does a Red Team Work?
Red Teams, although it may not seem like it, spend more time planning an attack than carrying out attacks. In fact, the Red Team is responsible for implementing a series of methods to gain access to a network. Red Teams are hired to test the effectiveness of the Blue Team by emulating the behavior of a real Black Team (cyber attackers) to make the attack as realistic and chaotic as possible.They use a wide variety of methods and tools to exploit and break down a network’s weaknesses and vulnerabilities. Among these, we might find phishing, vulnerability identification, firewall intrusion, etc. It is important to note that these teams will use all necessary means, according to the terms of the engagement, to gain access to a system. Depending on the vulnerability, they may deploy malware to infect a host or even bypass physical security controls by cloning access cards.Red Team Roles
- Red Teams emulate attackers, using the same or similar tools. Through these attacks, they aim to exploit security vulnerabilities in the organization’s systems and/or applications (exploits), use pivoting techniques (moving from one machine to another), and target the organization’s systems and/or applications.
- They carry out a process of emulating threat scenarios that an organization faces. They do this by analyzing security from the attackers’ perspective, to give the security team (Blue Team) the opportunity to defend against attacks in a controlled and constructive manner.
- Therefore, the Red Team serves as a test for the Blue Team, where the organization’s actual ability to protect its critical assets and its detection and response capabilities are evaluated, taking into account technological, process, and human factors.
Blue Team
How Does a Blue Team Work?
The Blue Team begins with an initial data collection, documents exactly what needs to be protected, and conducts a risk assessment. They then harden system access in a variety of ways. They also handle staff training on security policies such as stricter passwords and ensure that employees understand and follow security procedures.Monitoring tools are typically implemented to allow information about system access to be logged and verified to detect unusual activity. Blue Teamsperform periodic checks on the system, such as DNS audits, vulnerability scans of internal or third-party networks and capturing sample network traffic for analysis.Blue Team Roles
- They conduct constant monitoring, analyzing patterns and behaviors that deviate from the norm at the system, application, and human levels, as they relate to information security.
- They work on continuously improving security, tracking cybersecurity incidents, analyzing systems and applications to identify flaws and/or vulnerabilities, and verifying the effectiveness of the organization’s security measures.
How do the red and blue teams work together?
Finally, both teams must work together to plan, develop, and implement stricter security controls as needed.
Purple Team
The Purple Team exists to analyze and maximize the effectiveness of the Red and Blue Teams.The Purple Team coordinates the Red and Blue Teams to ensure their proper functioning and development
Functions of the Purple Team
The main objective of the Purple Team isto manage the organization’s security. They do this byconductingtests to verify the effectiveness of security mechanisms and procedures and to define/develop additional security controls to reduce the organization’s risk.For both companies and institutions, it is essential to implement security controls to minimize the risks of a cyberattack and protect the data they handle.What are the benefits of having this equipment?
- Strengthen your entire system. With Blue Team security testing and development, your system will become stronger and new, more effective security measures will be created.
- Creating an action plan. Using the Purple Team’s actions, you can create various action plans. You will be able to anticipate potential attacks or other IT issues identified by the Red Team’s attacks.
- Peace of mind. With the Blue and Red Team attacks and defenses, while there is always room for improvement, you’ll know your system is protected.
“Cyberattacks in Spain have increased by 125% over the past year, reaching 40,000 per day”Source: CyberSecurity News – 2021This increase in cyberattacks is caused by the rapid shift to the digital world by many companies that have been forced to make the change due to the pandemic. It has also been caused by the adoption of remote work, as many companies were not prepared for this change. That is why the implementation of cybersecurity is so important and vital for companies.
More than 1 million licensed users and more than 5 million recipients
Contact us for more information: info@tranxfer.com or through our social media: LinkedIn or Twitter