SHADOW IT – A HEADACHE
To begin understanding how we can help the CISO combat Shadow IT, we turn to the definition provided by the Gartner consultant to understand exactly what Shadow IT entails: consulting firm Gartner to understand exactly what Shadow IT consists of: “Shadow IT is any device, software, or IT service—generally cloud-based—that is used within an organization but is outside the control of that organization’s IT department or is used without its knowledge or approval”.
In other words, when an employee decides to use a cloud-based service without the company’s knowledge, they are engaging in Shadow IT. using a personal smartphone or laptop for work-related matters; sharing corporate documents via apps such as Dropbox, WeTransfer, or WhatsApp; connecting a USB drive brought from home to a work computer… Using shadow IT exposes the organization to security breaches and unwanted data leaks.
That is why we want to highlight the difficult situation faced by the CISO
The CISO is responsible for protecting without hindering employees’ day-to-day work and for providing tools that the business also approves of.
There is a syndrome called Cassandra Syndrome that defines the CISO’s difficult task. It goes like this: predicting without being heard and, when it happens, being judged for not having seen it coming …

How can we help the CISO in their duty to protect employees, the organization, suppliers, and shareholders?
Digitalization is changing the way organizations conduct their business and social relationships. A proven increase in productivity and efficiency, but with an unwanted side effect: an increase in, among many other things, email vulnerabilities, security gaps, and digital risk are becoming increasingly important.
IBM SECURITY HIGHLIGHTS THAT:
- 1 in 3 workers share and upload corporate data to third-party cloud applications.
- 1 in 4 employees log in to cloud solutions using their corporate username and password.
This can lead to significant security gaps exploited by cybercriminals to obtain company data. It can cause problems and expose the company to unanticipated risks. In these cloud-based applications, the data used is not protected appropriately or in accordance with the standards of the organization or its clients.
At Tranxfer, we want to address this issue by highlighting the tension between Raising Awareness and Prohibiting
We want to share with you the most popular Shadow IT tools for sharing, storing, and backing up the files that cause the most headaches for CISOs and corporate IT security departments:
- Google Drive
- Dropbox, Box
- OneDrive,
- WeTransfer,
- YouSendIT,
- FireDrive
- ShareFile
These are the applications most commonly used by workers, although there are many others such as Yandex Disk, Solidfiles, Freakshare, Filefactory, Copy, 4Shared, eFolder, Goodsync, Hightail, Zippyshare, and Mega.
The tools mentioned above are examples of shadow IT and expose us to GDPR penalties and data breaches, as well as putting us at risk from ‘bad actors’
BBVA’s former CISO said something in 2019 that we believe perfectly defines the situation at hand:
”Sharing information with third parties using a
sharing is like leaving your house keys in the door and hoping nothing ever happens”
former BBVA CISO – 2019
What risks does the company face by using Shadow IT tools?
The most common problems among companies that use Shadow IT tools are as follows:
- Data breaches
- GDPR non-compliance
- Malware Infection
How can non-compliance with regulations be harmful?
- Financial consequences resulting from penalties, depending on the size of the organization, ranging from 10 to 20 million euros or between 2% and 4% of the company’s annual revenue.
- Reputational consequences.
How can these risks be avoided?
We are making Tranxfer available to all organizations, regardless of their size, to ensure the secure flow of information and meet workplace needs under optimal conditions, supporting security managers in their work to protect the organization.
In 2020, the Naturgy Security Department defines us as:
‘’Tranxfer is the best corporate platform for eliminating shadow IT and the most secure for exchanging information’’
Naturgy Security Department – 2020

If Shadow IT is inevitable, bring it to light! And turn it into an opportunity
The radical approach to combating shadow IT is to block access to all non-corporate services. However, this may not always be realistic for all companies, especially in this new work environment where many employees are not in the office. Sometimes, Shadow IT itself, through applications used by employees, can help them do their jobs better, so a ban could impact business efficiency.
Tranxfer is the perfect tool for your employees as an alternative to WeTransfer and other platforms for sharing ATTACHMENTS AND LARGE FILES with maximum security guarantees and advanced features.
WHAT MAKES US AN ATTRACTIVE OPTION?
Easy to adopt and valued in business for its extra features
Available as a web version or as an email integration
Instead of viewing shadow IT as a threat, companies should see it as an opportunity to encourage employees to identify the applications they want to use. In this way, the IT department will be able to enable applications that comply with company rules or that can be used even if they break some rules. It is necessary to embrace the idea that users should explore new technologies, new tools, and new processes or services that facilitate their work and transform them into more efficient professionals in sales or operations within a supply chain.
WANT A FREE TRIAL? – Contact us for more information
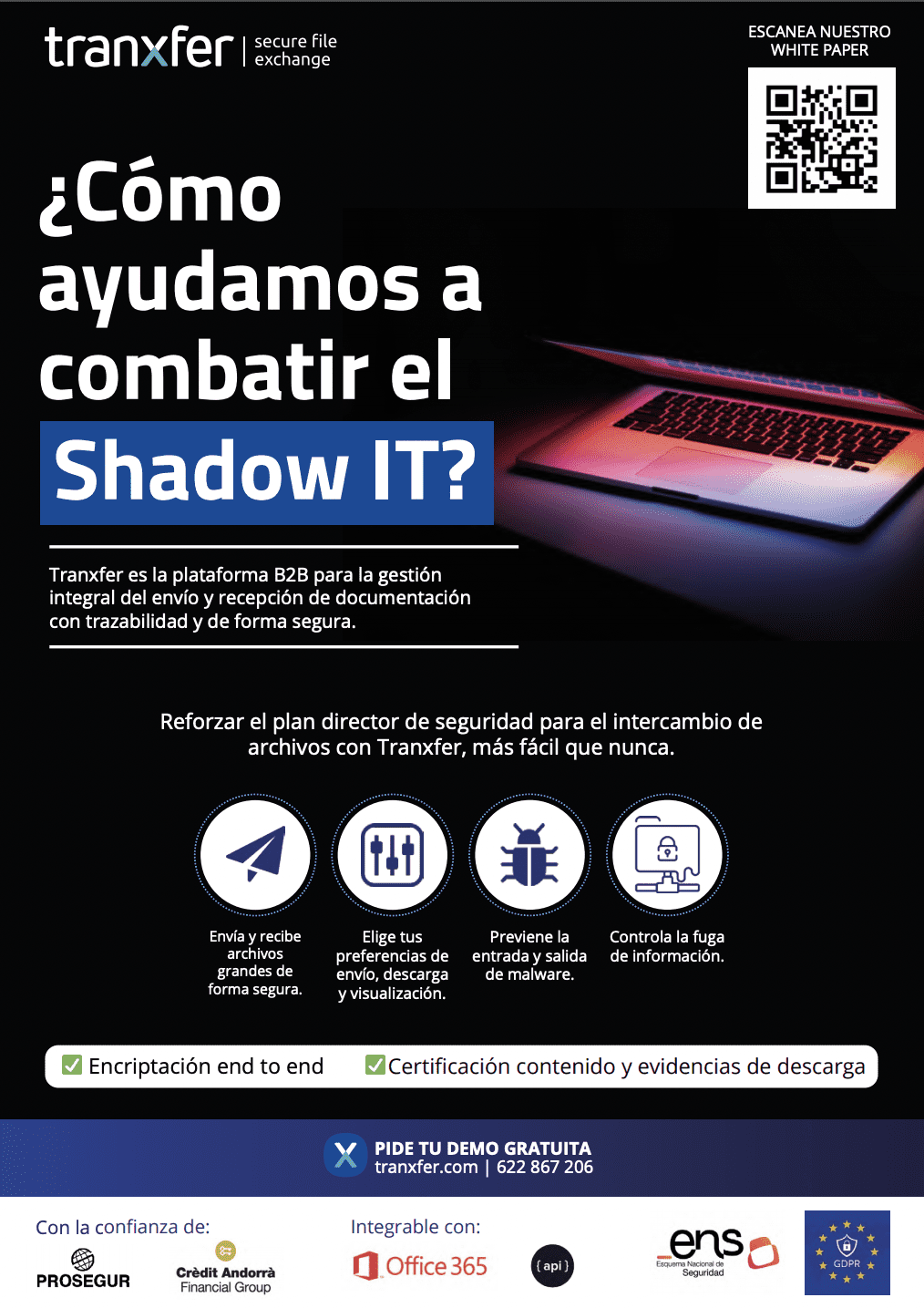
With TRANXFER, you can easily protect your organization:
- Send files and receive files with no size limit, securely. The tool offers traceability and continuous auditing; monitoring, read receipts, and tracking of views and/or downloads.
- Advanced security policies and an easy-to-use user and admin interface, available as a web version or O365 plugin.
- We offer APIs and plugins for integration with other systems
- We can integrate with SIEM, Active Directory and offer different deployment options
- Data breaches | GDPR non-compliance | Malware infiltration
The tool of choice for CISOs to combat shadow IT and strengthen their security director’s plan for file sharing
- Send and receive files securely
- Choose your delivery and
- display preferences
- Prevent malware from entering and leaving
- Controls data leaks
- End-to-end encryption
Over 1 million licensed users
Over 5 million recipients
Contact us for more information: info@tranxfer.com
Or through our social media: